We all like to think that we won’t fall for scams, whether it’s a Nigerian prince asking to share his wealth, or a dodgy pyramid scheme. The truth is however, many of us are still falling for scams and clicking on things we shouldn’t.
Email phishing remains the top infection vector for cyber criminals and they are effective at crafting legitimate looking emails at both random and targeted victims.
 |
| Example of a Phishing email |
To enhance the odds of a target falling for a phishing email, cyber criminals use a technique called Social Engineering which tries to manipulate, influence or deceive you into opening and clicking the email. The most common form of social engineering is a scam email copying the ‘look and feel’ of a well-known organisation that you would be expecting to hear from. Once you click on the link you are usually taken to a fake site where you are asked to enter personal details or your login information, or malware is installed on your computer.
The current top subject lines people fall for are:
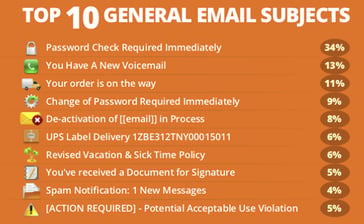
- Password Check Required Immediately 34%
- You Have A New Voicemail 13%
- Your order is on the way 11%
- Change of Password Required Immediately 9%
- De-activation of [[email]] in Process 8%
- UPS Label Delivery 1ZBE312TNY00015011 6%
- Revised Vacation & Sick Time Policy 6%
- You've received a Document for Signature 5%
- Spam Notification: 1 New Messages 4%
- [ACTION REQUIRED] - Potential Acceptable Use Violation 4%
These most clicked phishing emails, coupled with the fact that employees are actually performing worse this year in cyber security practices than last year, paints a troubling picture.
So what can you do?
Train your staff
Users are the last line of defense in your business. It doesn’t matter how great your security software is or how much you spend, all it takes is one misplaced click on an email and your whole system can be compromised.
Staff should be trained to pick out red flags and the techniques that hackers use to encourage people to give up valuable information.
Phish your staff
Regularly sending simulated phishing emails to employees reinforces their security training and keeps them on their toes with security top of mind.
Companies that have implemented white hat phishing and training have seen a significant drop in staff clicking on compromised emails.






Let Us Know What You Thought about this Post.
Put your Comment Below.